Lessons in Security From Those in The Know
Speakers/Moderators

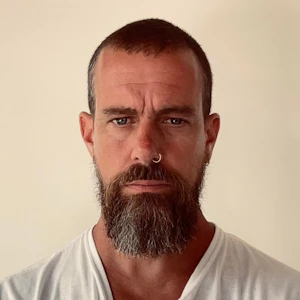
Justine Bone

Justine Bone

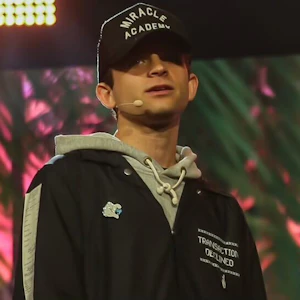
Garret Kelly

Garret Kelly

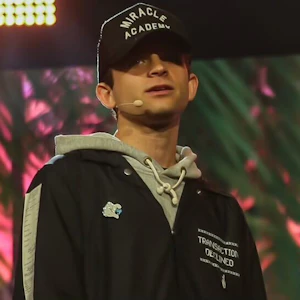
Erik Kellogg

Erik Kellogg
Previously, he served as a principal leader within Palo Alto Networks’ Unit 42, advising organizations on cyber risk, resilience, and incident response. Erik brings deep expertise in digital asset security, threat detection and response, and operating security at scale in high-risk, adversarial environments.

Alex Pruden

Alex Pruden
Alex is a former U.S. Army Green Beret who transitioned from military service to a career in blockchain and cryptocurrency after witnessing the profound challenges in conflict zones like Iraq, Afghanistan, and Syria. After earning an MBA from Stanford, he began his decade-long career in the industry at GGV Capital, Coinbase, and Andreessen Horowitz before joining Aleo as the first employee and scaling the organization as CEO to pioneer the first permissionless, privacy-preserving smart contract blockchain powered by zero-knowledge proofs.
Session
Overview
This security-focused discussion brought together Justine Bone of Crypto ISAC with Garret Kelly of Robinhood, Erik Kellogg of Binance.US, and Alex Pruden of Project Eleven to examine how Bitcoin and crypto companies manage cyber risk. The conversation emphasized that security is not a fixed end state, but an ongoing process of vulnerability management, prioritization, governance, and incident readiness.
The panel covered current threats such as software vulnerabilities, phishing, insider risk, and nation-state activity, including attacks aimed at employees and hiring processes. Speakers highlighted the need for defense in depth, stronger operational controls, and collaboration among security teams across the crypto industry.
A major theme was emerging risk, especially post-quantum cryptography and the long-term need for Bitcoin and other blockchain systems to prepare for quantum-capable attacks. The panel also discussed AI’s impact on security, including AI-driven offense at scale, defensive use cases for prioritization and tooling, and the challenges of safely integrating AI into enterprise systems.
The session framed Bitcoin security as a continuous risk management discipline that depends on technical rigor, transparency, leadership, and shared threat intelligence across the ecosystem.
All right. I think we are already over time, so I'm just going to jump right in. Folks, thank you so much for joining us this morning. We're really excited to be here at the kickoff of the Bitcoin conference. This is the security panel, so we're here to talk about what's going on with security and risk management as it relates to Bitcoin.
My name is Justine Bone. I'm the executive director of an organization called the Crypto ISAC. That's the Information Sharing and Analysis Center. We're a nonprofit and independent. We work with the security teams at the biggest crypto companies out there. We allow these security teams to come together in a trusted space on a security platform to share what we call cyber threat intelligence and swap notes about the risk landscape, the threat landscape, threat actors, incidents, vulnerabilities, and other issues that come up more than daily. It's continuous.
My career was spent in the cybersecurity industry. I came into crypto about three years ago. Before that, I was the chief information security officer at Bloomberg and at Dow Jones. I'm also an entrepreneur in the cybersecurity industry, so I've started a few cybersecurity companies. Like many, I started my career in government service in the public sector, and I'm able to leverage a lot of that experience bringing together these different companies within the Crypto ISAC.
I'm really grateful to be joined here today by a set of security leaders who are dedicating a lot of their time to securing the Bitcoin ecosystem. I'm going to allow the gentlemen here to introduce themselves, and then we'll get into our panel. Thank you so much. Alex.
Hey everyone. It's great to be here. I'm Alex Pruden. I'm the CEO of Project Eleven, which is an organization that does research at the intersection of quantum computing and post-quantum cryptography as it pertains to blockchains and digital assets, and then builds products around implementing post-quantum cryptography at institutions that have exposure to blockchain-based rails. That's what I do. I've been in crypto for about 11 years now.
Hello everyone. My name is Erik Kellogg. I'm the CISO of Binance.US. I've been there for a little over four years, but in technology security for almost 27 years now, a long time. I'm simply just the CISO at the exchange.
I'm Garret Kelly. I'm a principal software engineer and the CISO for Robinhood Crypto. I've been around for just over five years and was involved in the custody programs.
We've got a CEO founder and we've got two CISOs here, chief information security officers. Let's start with that. Erik, Garret, what exactly is a chief information security officer?
When people think about CISO, there are a couple different archetypes. People think of someone in more of a governance and regulatory oversight position, and I think that's an important role. Obviously you need governance and regulatory oversight for a company. But I also think there is a different archetype, which is the technical CISO, which is where I feel like I fit in. That is somebody who is deeply involved in all aspects of the products and the security of the systems.
I like to think that a technical CISO asks the question, so what? When somebody brings you insider knowledge or vulnerabilities externally, you need to be able to know how that fits into the entire stack and secure everything from top to bottom.
I've got a lot to do with the governance and compliance aspect, but I'm very much a technical CISO, hands on, very involved with the products and the teams, and just making sure that the operations are safe day to day.
It's a multifaceted set of responsibilities. When you're a chief information security officer, often CISOs come from very technical backgrounds. Maybe they're software developers, maybe they're security researchers. But as Garret pointed out, there's an important aspect to the responsibility that is explaining the impact of a security issue to their respective company.
If a vulnerability is discovered in a piece of hardware, software, or infrastructure, that question of “so what?” really drives a lot. It speaks to the larger responsibility, which is managing risk that the CISO participates in. Risk management, which can mean a lot of different things, including technology risk management, is really the day-to-day focus of a chief information security officer within your respective programs.
I was wondering if you could talk a little bit about vulnerability management and what that means. What does it mean to keep systems updated, and how does that relate to security issues that, especially in this generation of AI, are coming up over and over? How do you look at system maintenance and vulnerability management?
It's a really tough problem, especially for a company. The older a company gets, the more technical debt you have, period. Vulnerability management is the way that you take the stream of incoming issues and turn it into action if you need to. You assess the actual impact, assess the exposure, that kind of thing. It's very important, but it's also really easy to fall into naive patterns where you say, there's a vulnerability in a library, what do we do about it? At the end of the day, it might not even affect your stack, but you've got some vulnerability scanner somewhere that's pinging off of it, and now it's the most important thing in the world that you have to patch.
It's a balancing act, and it's one that a lot of companies spend a lot of money and time getting wrong in a lot of ways.
How do you learn about a vulnerability? How do you become aware that there's an issue that needs to be considered and addressed?
There are a couple of different ways. Some come through the front door. Some of it will just be vulnerability feeds for software packages. Then you have to take that list of software packages, compare it to the list of software packages that you actually run in your infrastructure, stitch them together, and figure out if that's something you're affected by.
Other times you'll have a bug bounty program, and somebody is reporting to you something externally exploitable. That's another way you'll get vulnerabilities. Sometimes it'll just be contacts or researchers or intelligence from the field. If you're working with other teams, you might hear from another CISO or another group about a specific class of threat that's coming up.
When you realize that a vulnerability impacts your business to the point that it needs to be addressed, what is the process of fixing it?
It really depends on the vulnerability. Some vulnerabilities might be infrastructure. Some might be actual software packages. A lot of it can be as simple as updating manifests and rolling out new software to the rest of the fleet. But some of it might be, now you have to work with your cloud provider because the cloud provider is vulnerable to this vulnerability. What are you going to do about it? If they have a six-month timeline for their remediation, it really comes down to the specifics.
There is one size fits most, which is the software package needs to be updated and there's a published patch for it. But in some cases, there won't be a patch, and you have to think, how do we limit the exposure to this vulnerability? How do we make sure that this can't actually affect our infrastructure or any users?
The reason I'm hammering on that is because this is a continuous process that never ends. You're never done in cybersecurity. There's always more that needs to be triaged, analyzed, and considered in terms of business priorities. It's a risk assessment. This is a journey. There's a misconception out there sometimes that security is a state we can reach and then we're done, and it's very much not that. Erik, any thoughts?
I agree. It'll never end. One of the things that you need to solve as the CISO is eliminating noise, like which vulnerabilities to actually pay attention to versus what you don't. You can have something critical that is buried beneath a lot more layers of controls, so you have to prioritize. You will get to that vulnerability at some point, but maybe not as quickly.
With AI in the mix, those are just becoming more and more constant. Developing our in-house tools to keep eliminating the noise so we know what to focus on first is pretty critical to vulnerability management. I also think one piece of vulnerability management is the human aspect. There is no patch for humans.
The employees are really used to us hammering this home. We're always testing them. We're always throwing really hard phishing tests and things, and just hammering home that the security of the company is every employee's responsibility, because everyone could be targeted.
We're going to get on to some emerging threats, but right now we're talking about current-day threats. As you can get a sense, security vulnerabilities in software are deeply technical things. But even more serious than that are human vulnerabilities. This is another day-to-day challenge that CISOs and security leaders are really challenged with.
We've got the founder of a Layer 1 here now tackling post-quantum cryptography, which we'll talk about in a second. We've got an exchange, Binance.US, and we've got Robinhood. Each of these members and stakeholders has their lens on security. But there's one thing that I hear every single day at Crypto ISAC: nation-state threats targeting humans. Anyone got anything to offer as it relates to nation-state threats, DPRK, or others?
The people problem is security. Security has to be everybody's problem, but at the same time, security has to not depend on any individual. A lot of what we're doing in security as an industry comes down to prevention in depth. If you are vulnerable to a single person walking in the door and getting a corporate laptop, and that ruins your key management infrastructure, that's bad. That means you only have to get one false employee to ruin your entire day or your entire operation.
What we're seeing right now is that there are people who are going to get through the front door eventually. They're going to become employees eventually, and they are going to try to work against you and your infrastructure from the inside. It's more important now than ever to have extreme depth and extreme preventative measures, because in crypto you can't take back money from somebody else's wallet. It's extremely important that one person doesn't ruin your entire operation.
I agree with that. For us, it is this whole paradigm shift now of hiring and the processes you have to put in place. Even after that, you need constant monitoring. It's a tough challenge to feel like someone is going to get through that door, and it's still a pretty new problem. There is no magic bullet for this yet.
This is where it really comes in: different CISOs, different profiles of potential DPRK or confirmed DPRK threat actors. I really hate this problem as a CISO because it's such a hard one to solve.
It's very hard to solve human weaknesses.
Nation-state level attacks are something I think about a lot, mainly because in the quantum world, the only entities with the resources to fund these efforts are nation-states, directly or indirectly. The companies building the systems are often in these government programs.
Nation-states are unique threat actors. They're not necessarily economically driven all the time. As it pertains to Bitcoin and crypto, different nation-states view it in different ways in terms of what kinds of attacks they would potentially consider. Their objectives could be beyond simply economic gain. It could be disrupting a system that serves as a potential alternative to people who live in a country, to circumvent capital controls or gain financial freedom against repression that the very same government is applying to its citizens.
It's a complex factor that CISOs have to consider, and I think it will get more complex as we enter the era of quantum computing as a potential weapon.
Hopefully that helps demonstrate that a CISO not only has to have the technical depth that we talked about, but also these human threats and other types of risk that we're thinking about on the operational side, even on the physical security side, where we've seen executives being targeted at crypto companies and beyond. There is a wide set of responsibilities that fall under the mandate of a security leader in a crypto company.
These are day-to-day threats that we're tackling and fires we're putting out. But we're also looking over the horizon at emerging threats. One of them is post-quantum cryptography and resilience as compared to pre-quantum cryptography. Clearly this is not part of my day to day yet. But for Alex here it is. Alex, would you talk the audience through what you see this all about, and why this is a security consideration as we look forward to the resilience of Bitcoin infrastructure in the future?
Just a quick clarification: I don't actually run a Layer 1. I do not have a Lambo parked anywhere in this expo, so don't look for it.
Quantum computers potentially are going to be great for many things, but one thing that we know they can do is break basically the foundation of modern cryptography. As that pertains to Bitcoin in particular, the way we transfer Bitcoin back and forth between each other is with digital signatures. If I have the private key, I can sign a message with that private key, and then I have this signature that's associated with a public key, which can be my address. That's how the network basically tracks who owns what.
With a quantum computer, what you do is basically go the wrong way on that one-way road. With the public key, or someone's address, you can effectively go backwards and get their private key, and then sign messages on their behalf. That's a simple way to think about it. That's obviously potentially very devastating for a network that's built around cryptography to define what ownership means.
The natural, inevitable question that always comes up is: when? The “when” question is tied back to my comments earlier around nation-states. Nation-states have been pursuing this for a long time for both scientific as well as intelligence reasons.
One thing I want to point out is that talking about quantum should not be viewed as FUD. I'm very happy to be on this panel with these CISOs who think about risk more day to day. This is just a risk. It's a risk that we have to consider in terms of how likely it is and how big it is. Quantum is one more risk.
With regard to timelines, because this can effectively be used to break cryptography that is also used to secure very sensitive information, there is not a lot of incentive for the folks funding it to reveal how far or not far along they are. This uncertainty around the risk is one of the biggest problems.
On one hand, we have time-tested cryptography used in the Bitcoin network. In some ways, it's the most impressive cryptography on the planet. There are trillions of dollars of value, and it has never been broken. Nothing in the realm of cryptography has anything close to that track record. It's hard because you don't want to throw away what has worked, but there is a risk that it may not work against this specific kind of weapon. Again, this is just a risk that we have to consider among many other risks and triage appropriately.
We talked a little bit about software updates as they relate to vulnerabilities and patch management. There's also a concept of updating Bitcoin to be quantum resilient. Am I right?
Exactly. All blockchains, including Bitcoin, are going to have to upgrade the underlying cryptography that they use. Because this is a decentralized network, where it's not your keys, not your crypto, every user or every wallet has to also migrate to that new secure cryptography. It's a two-step process.
So every user is going to have to migrate to this newly upgraded Bitcoin infrastructure to be quantum safe. When we talk about impact, this will be an institutional impact, but it will also be a user, investor, and consumer impact as well, dealing with this particular type of threat.
My question to you is, who do you talk to about this when you start considering it? We talked backstage. We're talking to quantum security experts and trying to get a feel for what's available. What should we be doing now? What do we need to be thinking about as time goes on? What are the indicators that this might be getting closer? Where do you get those insights? Who is going to be making those decisions?
My answer would be that, in risk, we want to mitigate the potential worst-case outcome. I would advocate for everyone in the industry, including the companies you work for, to be proactive in preparing for that sort of risk, but not overly so. This doesn't have to be a fire drill. We don't need to throw everything out that has worked. But proactive preparation, like it sounds like exactly what you're describing, is absolutely the right approach.
Thankfully, I'm very happy to say I was here last year and I was talking about this, and everyone kind of gave me weird looks. This year, I think it's much more of a topic, and I'm happy that the conversation is happening.
One of the more interesting risk parts of the post-quantum discussion is that it's not going to happen instantaneously. It's not going to be next Tuesday and that's it for elliptic curve signatures. But at the same time, you have to ask yourself each year going forward, is this the year, and are you 100% sure of that? Because in the year that you are not 100% sure, you kind of need to do the migration. If you are wrong, the cost of being wrong is tragic. The cost of being right is that you get to protect the funds going forward.
It's this constant balance. Being where we are right now and not having the world's clearest view of when being less than 100% sure is going to be puts us in a very tough position for risk management. It doesn't feel like a fire drill, but it is coming. That's what it feels like.
I agree.
It's a panel, so we need to talk about AI. In this case, I'm just going to throw it over to the three of you. AI for offense, security offense, AI for defense. There's a lot of AI for operational efficiency, which is certainly what we're doing at the Crypto ISAC. Alex, I want to start with you. Thoughts on the convergence of AI and crypto infrastructure?
AI is certainly not my area, so I don't want to pretend like I'm an expert at all. But one area that's maybe underappreciated or talked about is that there are a lot of models out there that people are focused on solving math problems, winning various awards, or solving long-term unsolved problems. Ultimately, cryptography is math. I think there's a really rich, unexplored area to apply these models to developing, or at least testing, new and upcoming cryptography like post-quantum cryptography, so that we can help gain confidence in it. When the time comes for these gentlemen to migrate their systems, maybe they can feel more confident that it has been battle tested in a way that it couldn't have been before the era of AI.
This concept of cryptographic algorithm agility matters now. We've been stuck on a few proven algorithms for many decades. NIST has come out with post-quantum resilient algorithms to take us forward. But to your point, Alex, with AI and its input, maybe future cryptographic algorithms that humanity has not identified yet will emerge. We need to be able to be agile enough to roll our infrastructure over to these newer algorithms and maybe not get quite so married to one particular algorithm as we have been in the past.
I think it's a little different for us. For me, at the exchange, the industry at large is seeing a huge uptick in AI-driven attacks, creating more noise, and we are trying to leverage AI to eliminate the noise and focus on what's really important and what we need to spend our time on. Internally, we're trying to ramp up the tooling for the business and for all aspects of the business, but keeping that secure so we're using AI responsibly. It's a different challenge and use case for us. I love it and I hate it.
There are a lot of CISOs out there who are really challenged with internal integrations, leveraging AI, and all of the API permission complexity that goes along with that. There are a few CISOs who are members of the Crypto ISAC who share their headaches with me. I think that's a real challenge right now: integrating a lot of this AI infrastructure and making sure it's done safely for an enterprise.
I like the model of thinking of AI as increasing the intensity, but not necessarily the complexity, of the security problem. There was a recent publication about some attacks that occurred in South America. The attackers were using AI as part of their toolkit. If you look at the traces, it's not that the attackers were super intelligent, but the AI was persistent and the AI didn't sleep. They have tools where they can kick off some agents, go to bed, and come back and take a look at the output.
I think this is what we're going to end up facing: not necessarily super-skilled attackers, but so many more attackers who have $2 worth of token spend to throw at a company. That's very different from the quantum side of things, where it has to be somebody who has $2 billion to throw at the problem. But it's definitely still a real and present threat to the industry.
Security offense at scale, thanks to AI. What about defense? Within the security vendors that are out there, have you seen much in terms of leveraging AI to improve defense?
Absolutely. Even internally, we're using AI for some of our internal prioritization and security operations. We have some filtering that happens. A lot of vendors are fully on the AI train in terms of using it for defense.
I think there is still a trade-off being made. Yes, you could probably find interesting things using AI in your defense stream, but at the same time, you're also going to spend a lot of money on tokens doing that. Having a first tier of high-signal prioritization that is rules- or policy-based is still very important before you hand it off to the models to assess. But absolutely, I think it is and will be the future of a lot of the defense aspects of security.
We've seen the tools just get better and better. I think this is going to make the market for defense tools a lot tighter and really up the game across the board. We also start to leverage it to build tools that are specific to our business and how we operate day to day. We're actually able to level up our internal security controls and measures. There are no tools that will absolutely hit every need for us, so it's helped us build our own tooling, which is nice.
To customize to your own risk culture.
Yeah.
On that note, we're coming up to our close. I'm going to go down the line here and give you all a quick chance to give the folks in the room a reason to feel confident in the future and the resilience and security of crypto, and Bitcoin specifically. Alex, any thoughts?
Bitcoin is an amazing thing. In many ways, it is a testament to what cryptography can do, and applied cryptography. The amount of money that has been secured for as long as it has, and the way that it has with such decentralization, is spectacular. I have no doubt whatsoever that Bitcoin will survive any threats that get thrown at it in some form. Obviously there is work to be done to mitigate these threats, but I think Bitcoin specifically, and blockchain-based rails generally, are here to stay in finance.
As much as there are bad guys out there, there are also good guys who care, who want to keep this safe, who really believe in Bitcoin and what it stands for and what we can do with it. It's not just bad people out there. There are also good guys on the fight team.
It's definitely one of the technologies that has stood the test of time and has evolved over time. It has been really fascinating to see over the years. I do think Bitcoin will have a future.
Hopefully that gave you a bit of insight into the complexity and multifaceted aspects of the day-to-day life of security leaders in the crypto and Bitcoin ecosystems. Security is not an end state. It is not a goal that we reach and then we're done. It is risk management. It is a continuous journey.
Just as you are all managing risk if you invest in Bitcoin or otherwise leverage Bitcoin, you're making risk-informed decisions based on the information available to you. So do these guys. They belong to the Crypto ISAC: Robinhood, Binance.US, Project Eleven, and others. You can check out Crypto ISAC. We have the most mature security teams in the industry working together day to day.
My takeaway for you all would be, please don't think of things like a code audit as a promise of security. No, it's a journey of risk management. The signal you should be looking for is leadership and governance like this in the platforms and infrastructure you're looking at. It's this kind of leaning in, thought around risk assessment, and transparency. By the way, the fact that these leaders got up on stage today and talked about these security programs, that's what you want to be looking for.
Thank you so much for joining us. Enjoy the conference.
Similar
Sessions
Lessons in Security From Those in The Know

Justine Bone

Justine Bone

Garret Kelly

Garret Kelly

Erik Kellogg

Erik Kellogg
Previously, he served as a principal leader within Palo Alto Networks’ Unit 42, advising organizations on cyber risk, resilience, and incident response. Erik brings deep expertise in digital asset security, threat detection and response, and operating security at scale in high-risk, adversarial environments.

Alex Pruden

Alex Pruden
Alex is a former U.S. Army Green Beret who transitioned from military service to a career in blockchain and cryptocurrency after witnessing the profound challenges in conflict zones like Iraq, Afghanistan, and Syria. After earning an MBA from Stanford, he began his decade-long career in the industry at GGV Capital, Coinbase, and Andreessen Horowitz before joining Aleo as the first employee and scaling the organization as CEO to pioneer the first permissionless, privacy-preserving smart contract blockchain powered by zero-knowledge proofs.
Lessons in Security From Those in The Know
Speakers/Moderators

Justine Bone

Justine Bone

Garret Kelly

Garret Kelly

Erik Kellogg

Erik Kellogg
Previously, he served as a principal leader within Palo Alto Networks’ Unit 42, advising organizations on cyber risk, resilience, and incident response. Erik brings deep expertise in digital asset security, threat detection and response, and operating security at scale in high-risk, adversarial environments.

Alex Pruden

Alex Pruden
Alex is a former U.S. Army Green Beret who transitioned from military service to a career in blockchain and cryptocurrency after witnessing the profound challenges in conflict zones like Iraq, Afghanistan, and Syria. After earning an MBA from Stanford, he began his decade-long career in the industry at GGV Capital, Coinbase, and Andreessen Horowitz before joining Aleo as the first employee and scaling the organization as CEO to pioneer the first permissionless, privacy-preserving smart contract blockchain powered by zero-knowledge proofs.
How Real is the Quantum Threat?

Alex Thorn

Alex Thorn

Alex Pruden

Alex Pruden
Alex is a former U.S. Army Green Beret who transitioned from military service to a career in blockchain and cryptocurrency after witnessing the profound challenges in conflict zones like Iraq, Afghanistan, and Syria. After earning an MBA from Stanford, he began his decade-long career in the industry at GGV Capital, Coinbase, and Andreessen Horowitz before joining Aleo as the first employee and scaling the organization as CEO to pioneer the first permissionless, privacy-preserving smart contract blockchain powered by zero-knowledge proofs.
How Real is the Quantum Threat?
Speakers/Moderators

Alex Thorn

Alex Thorn

Alex Pruden

Alex Pruden
Alex is a former U.S. Army Green Beret who transitioned from military service to a career in blockchain and cryptocurrency after witnessing the profound challenges in conflict zones like Iraq, Afghanistan, and Syria. After earning an MBA from Stanford, he began his decade-long career in the industry at GGV Capital, Coinbase, and Andreessen Horowitz before joining Aleo as the first employee and scaling the organization as CEO to pioneer the first permissionless, privacy-preserving smart contract blockchain powered by zero-knowledge proofs.
Other
Speakers

Michael Saylor

Michael Saylor

Todd Blanche

Todd Blanche
Biography of Deputy Attorney General Todd Blanche
The Honorable Todd Blanche is the 40th Deputy Attorney General of the United States, overseeing the work of the 115,000 dedicated employees who fulfill the Department of Justice’s mission at Main Justice, the FBI, DEA, U.S. Marshals, ATF, and 93 U.S. Attorney’s Offices.
Todd began his career at the Department where he served for over fifteen years in a variety of capacities, including as a contractor, a paralegal in the Criminal Division, and at the United States Attorney’s office for the Southern District of New York where he eventually became an AUSA and later a supervisor.
After leaving the Department, Todd worked as a criminal defense attorney that included representing President Donald Trump in three of the criminal cases brought against him in 2023 and 2024.
Following President Trump’s historic return to the White House, the President appointed Todd to work alongside Attorney General Pam Bondi to make America safe again. At the DOJ, Todd is working tirelessly to implement President Trump’s priorities that include confronting illegal protecting American businesses from fraud.
Todd has been married to his wonderful wife Kristine for nearly thirty years, is a father and grandfather.

Paul Atkins

Paul Atkins
Prior to returning to the SEC, Chairman Atkins was most recently chief executive of Patomak Global Partners, a company he founded in 2009. Chairman Atkins helped lead efforts to develop best practices for the digital asset sector. He served as an independent director and non-executive chairman of the board of BATS Global Markets, Inc. from 2012 to 2015.
Chairman Atkins was appointed by President George W. Bush to serve as a Commissioner of the SEC from 2002 to 2008. During his tenure, he advocated for transparency, consistency, and the use of cost-benefit analysis at the agency. Chairman Atkins also represented the SEC at meetings of the President’s Working Group on Financial Markets and the U.S.-EU Transatlantic Economic Council. From 2009 to 2010, he was appointed a member of the Congressional Oversight Panel for the Troubled Asset Relief Program.
Before serving as an SEC Commissioner, Chairman Atkins was a consultant on securities and investment management industry matters, especially regarding issues of strategy, regulatory compliance, risk management, new product development, and organizational control.
From 1990 to 1994, Chairman Atkins served on the staff of two chairmen of the SEC, Richard C. Breeden and Arthur Levitt, ultimately as chief of staff and counselor, respectively. He received the SEC’s 1992 Law and Policy Award for work regarding corporate governance matters.
Chairman Atkins began his career as a lawyer in New York, focusing on a wide range of corporate transactions for U.S. and foreign clients, including public and private securities offerings and mergers and acquisitions. He was resident for 2½ years in his firm's Paris office and admitted as conseil juridique in France.
A member of the New York and Florida bars, Chairman Atkins received his J.D. from Vanderbilt University School of Law in 1983 and was Senior Student Writing Editor of the Vanderbilt Law Review. He received his A.B., Phi Beta Kappa, from Wofford College in 1980.
Originally from Lillington, North Carolina, Chairman Atkins grew up in Tampa, Florida. He and his wife Sarah have three sons.

Mike Selig

Mike Selig
Chairman Selig brings to the role deep public and private sector experience working with a wide range of stakeholders across agriculture, energy, financial, and digital asset industries, which rely upon and operate in CFTC-regulated markets.
Prior to his leadership at the CFTC, Chairman Selig most recently served as chief counsel of the Securities and Exchange Commission’s Crypto Task Force and senior advisor to SEC Chairman Paul S. Atkins. In this role, Chairman Selig helped to develop a clear regulatory framework for digital asset securities markets, harmonize the SEC and CFTC regulatory regimes, modernize the agency’s rules to reflect new and emerging technologies, and put an end to regulation by enforcement. He also participated in the President’s Working Group on Digital Asset Markets and contributed to its report on “Strengthening American Leadership in Digital Financial Technology.”
Prior to government service, Chairman Selig was a partner at an international law firm, focusing on derivatives and securities regulatory matters. During his years in private practice, he represented a broad range of clients subject to regulation by the CFTC, including commercial end users, futures commission merchants, commodity trading advisors, swap dealers, designated contract markets, derivatives clearing organizations, and digital asset firms. Chairman Selig advised clients on compliance with the Commodity Exchange Act and the CFTC’s rules and regulations thereunder, including in connection with registration applications and obligations, enforcement matters, and complex transactions.
Chairman Selig earned his law degree from The George Washington University Law School and was articles editor of The George Washington Law Review. He received his undergraduate degree from Florida State University.

David Bailey

David Bailey

Eric Trump

Eric Trump
Mr. Trump also serves as Executive Vice President of The Trump Organization, where he oversees the global management and operations of the Trump family’s extensive real estate portfolio. This includes Trump Hotels, Trump Golf, commercial and residential real estate, Trump Estates, and Trump Winery. Known for his hands-on leadership and strong market instincts, he has played a key role in expanding the company’s presence across major U.S. and international markets.
A globally recognized business leader and public figure, Mr. Trump is a prominent advocate for Bitcoin and decentralized finance. He is a co-founder of World Liberty Financial, a decentralized finance (DeFi) platform, and serves on the Board of Advisors of Metaplanet, Japan’s largest corporate holder of Bitcoin.
Beyond his business activities, Mr. Trump has helped raise more than $50 million for St. Jude Children’s Research Hospital in the fight against pediatric cancer, a philanthropic mission he began at age 21.
Mr. Trump earned a degree in Finance and Management from Georgetown University. He currently resides in Florida with his wife, Lara, and their two children. He is also the author of Under Siege, his memoir published in October 2025.
Jack Mallers
Jack Mallers
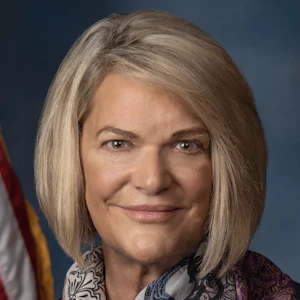
Cynthia Lummis
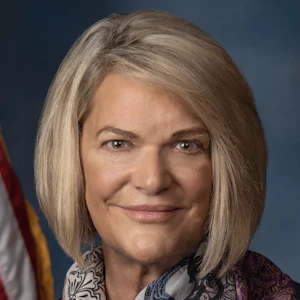
Cynthia Lummis
As the first-ever Chair of the Senate Banking Subcommittee on Digital Assets, Senator Lummis is the architect of the legislative framework shaping America's digital asset future. She introduced the landmark Lummis-Gillibrand Responsible Financial Innovation Act, the first comprehensive bipartisan crypto regulatory framework in Senate history. She co-authored the GENIUS Act — the first federal stablecoin law ever enacted — and introduced the BITCOIN Act, which would establish a U.S. strategic Bitcoin reserve of up to one million BTC. She is leading the Clarity Act, which will bring long-overdue regulatory certainty to the digital asset industry. She has also championed digital asset tax reform, including a de minimis exemption for small transactions and equal tax treatment for miners and stakers.
Known as Congress' "Crypto Queen," Senator Lummis represents Wyoming — a state she has helped build into one of the most digital asset-friendly regulatory environments in the nation. Before serving in the Senate, she served 14 years in the Wyoming Legislature, eight years as Wyoming State Treasurer, and eight years in the U.S. House. She is a three-time graduate of the University of Wyoming.
Her work represents a crucial bridge between traditional financial systems and the emerging digital economy, ensuring America leads the world in financial innovation while protecting the individual freedoms that define it.

Adam Back

Adam Back

Amy Oldenburg

Amy Oldenburg

David Marcus

David Marcus

Matt Schultz

Matt Schultz

Fred Thiel

Fred Thiel
Throughout his career, Mr. Thiel has consistently driven rapid growth and created substantial shareholder value. Prior to MARA, Mr. Thiel served as the CEO of two other public companies, Local Corporation (NASDAQ: LOCM) and Lantronix, Inc (NASDAQ: LTRX). He has successfully raised billions in equity and debt through private and public offerings, led companies through IPOs, executed high-value exits to strategic and financial acquirers, and implemented effective M&A and roll-up strategies.
Mr. Thiel attended the Stockholm School of Economics and executive classes at Harvard Business School, and is fluent in English, Spanish, Swedish, and French. Mr. Thiel is the Chairman of the Board for Oden Technology, Inc. and is active in Young Presidents’ Organization where he has led initiatives in both the FinTech and Technology Networks.
A recognized voice in the industry, Fred frequently shares his insights on energy and technology with major media outlets like Bloomberg TV, CNBC, and FOX Business, contributing to vital discussions about the future of these sectors.

Tim Draper

Tim Draper
He is a supporter and global thought leader for entrepreneurs everywhere, and is a leading spokesperson for Bitcoin and decentralization, having won the Bitcoin US Marshall’s auction in 2014, invested in over 50 crypto companies, and led investments in Coinbase, Ledger, Tezos, and Bancor, among others.

Afroman